Cybersecurity
Your internal security team is sharp. Even the best teams, though, can hit a wall. When threat levels rise, compliance deadlines loom or your team is stretched too thin, reinforcements can make all the difference. Many organizations strengthen their defenses through cybersecurity staff augmentation, bringing in outside expertise to meet challenges head-on. At Afidence, we…
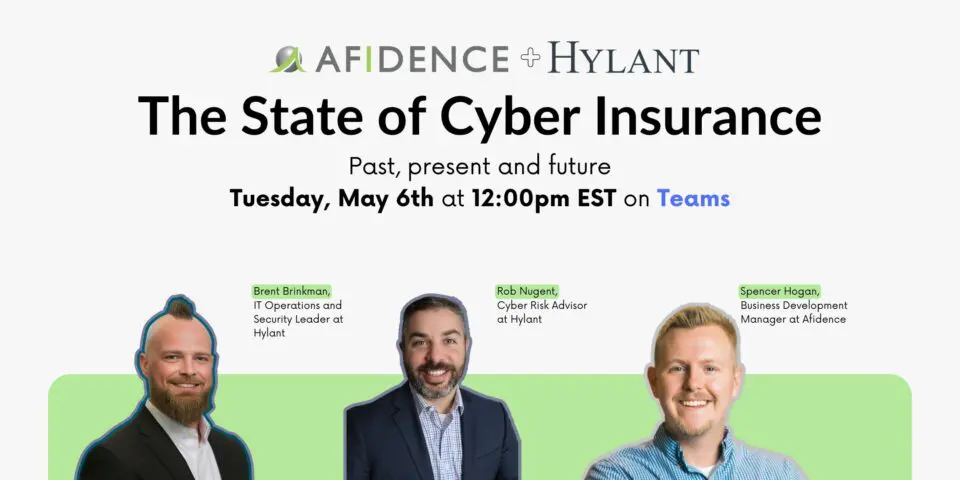
Read MoreJoin us for a virtual event on The State of Cyber Insurance—designed to help business and IT leaders navigate the evolving cyber insurance landscape. You’ll learn what cyber insurance is, why it matters, how it’s priced, and the top claims companies face today. We’ll also cover the critical security controls insurers require now, and explore…
Read MoreThe Cybersecurity Maturity Model Certification (CMMC) is a critical framework for businesses that work with the Department of Defense (DoD). It ensures that contractors and subcontractors meet essential cybersecurity requirements to protect controlled unclassified information (CUI). CMMC readiness and gearing up for compliance may seem complex, but with the right approach, your business can take…
Read MoreThe methods of cybersecurity attacks are continually advancing, which means they are becoming harder to detect. One that’s evolving at a particularly rapid pace is vishing attacks. This type of malware needs to be on your radar. Vishing, short for “voice phishing” is a type of attack where cybercriminals manipulate unassuming people over the phone…
Read MoreCybercriminals and hackers can find ways into your systems, networks, applications and more with just a little bit of work. One window slightly cracked or a door left barely ajar is all they need. Do you know if the windows and doors to your entire IT infrastructure are shut and locked? If not, you can…
Read MoreYour organization’s most critical piece of your network security strategy is a firewall. Your firewall acts as a barrier between your internal network and potential external threats. It’s vital for keeping your sensitive information safe and maintaining network integrity. Unfortunately, many organizations fall prey to these seven mistakes in firewall management. These errors could make…
Read MoreAre you concerned about the potential risks to your business in the instance of a data breach? How confident are you that your business is meeting all regulatory compliance requirements and data governance standards? Do you have the productivity tools, like Microsoft 365 administration, to overcome these challenges, but don’t know how to optimize them? …
Read MoreAre you ready to equip yourself with the knowledge and technical insights necessary to navigate the digital landscape easily and securely? In February, Afidence hosted a dynamic panel of industry leaders eager to share their real-world experiences and practical advice on harnessing the power of AI responsibly and securely. In case you missed it, check…
Read MoreThis past March, Afidence had the honor of presenting on the MITRE ATT&CK and D3FEND Frameworks at the Ohio Information Security Conference (OISC) hosted by Technology First. It was enlightening to be surrounded by other experts in cybersecurity and empower like-minded professionals with the knowledge to map D3FEND countermeasures and apply ATT&CK techniques to help…
Read MoreCyber insurance is like a safety net for your business in the digital world. It’s there to protect you from the unexpected, whether it’s a data breach, a cyberattack or even a ransomware attack. Just like you wouldn’t leave your home without locking the doors, cyber insurance ensures that your business is safeguarded against known…
Read More